 Do you run multiple SAP systems in a hybrid landscape? Are you worried about how you can protect them in real time above and beyond the authorization level? A variety of challenges can arise in such situations, because the implementation of security-relevant measures is time and resource-intensive.
Do you run multiple SAP systems in a hybrid landscape? Are you worried about how you can protect them in real time above and beyond the authorization level? A variety of challenges can arise in such situations, because the implementation of security-relevant measures is time and resource-intensive.
Keeping track of the big picture takes effort
When it comes to protecting multiple SAP systems, you need to have a continuous overview of the security status of the involved system landscapes. Various lists in a variety of media have to be reconciled, complex analyses of log files with security-relevant content have to be documented, and last but not least, other projects that are running alongside day-to-day business – such as SAP rollouts – also vie for attention. Accordingly, sufficient staff capacity has to be available to assess and implement security measures.
Full transparency and monitoring in real time for DÜRR IT Service GmbH
After commissioning an independent audit of its SAP systems to determine the current state of its system landscape, DÜRR IT Service GmbH faced these exact challenges. The DÜRR Group consists of three group divisions with some 16,500 employees in 116 locations around the world. The SAP Basis team is responsible for around 60 SAP systems in three individual system landscapes.
The company aimed to procure a tool that supported the hardening of the system landscapes through policies, while still allowing individual adjustments. The primary factors for DÜRR:
- Real-time monitoring of log files with immediate alerting of the persons responsible when potentially critical activities are detected
- Direct forwarding of the log files to an existing SIEM tool
- The possibility to conduct regular system audits and to analyze security trends
- Transparent portrayal of all incoming and outgoing connections in the SAP system landscape; the tool in question would serve as the central starting point and provide an overview of the full system security
- The company also wanted simple, intuitive usability
Implementing the requirements with support from the SAST SUITE
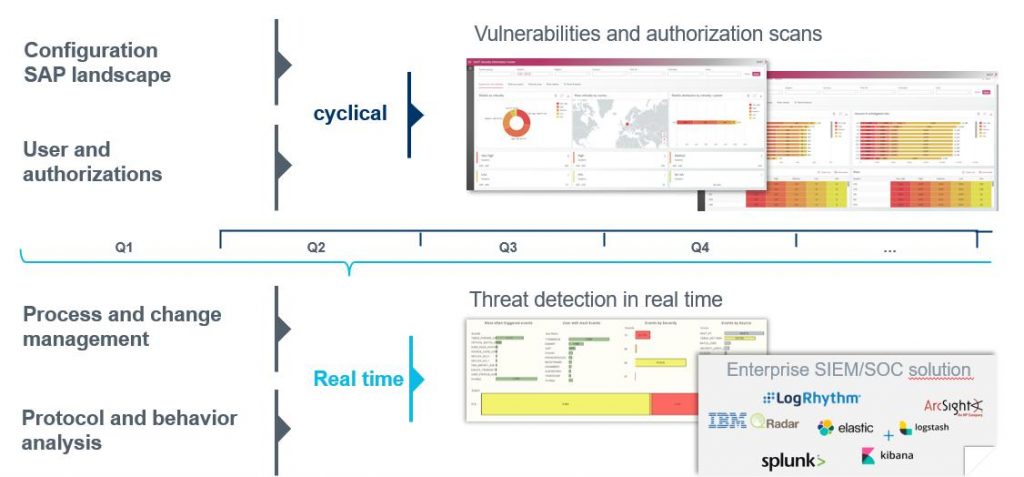
To achieve these goals, our project team implemented two components: a cyclical audit plan that detects vulnerabilities in the system and in the authorization area and real-time monitoring that identifies attacks in progress and alerts the persons responsible, who can then take the appropriate countermeasures.
The SAST Security Information Center shows the security status of all SAP systems at a glance. The current data is displayed at all times, in line with your individual audit strategy. The trend analysis lets you determine whether hardening your SAP systems will result in reduced risks and shows you where additional changes should be made.
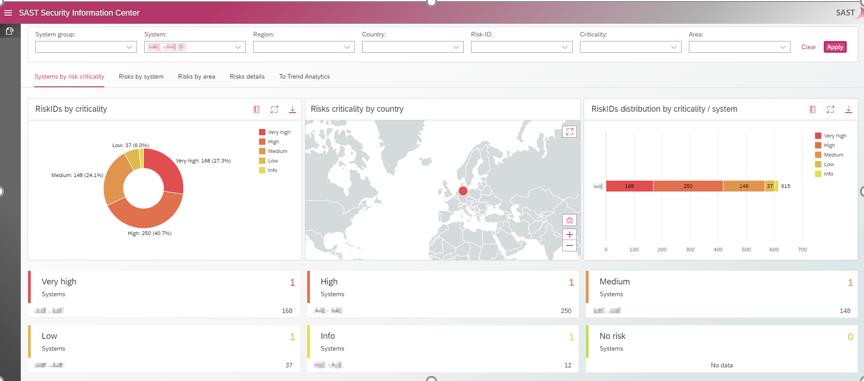
All risks are classified by their criticality and the many filter options make it easy for you to identify and eliminate individual vulnerabilities. The risks can be displayed by area and thanks to the tool’s transparency, you not only see how many critical risks exist, but also how many of your users are affected. The displays in the SAST Security Information Center are also user friendly and can be customized to your individual needs.
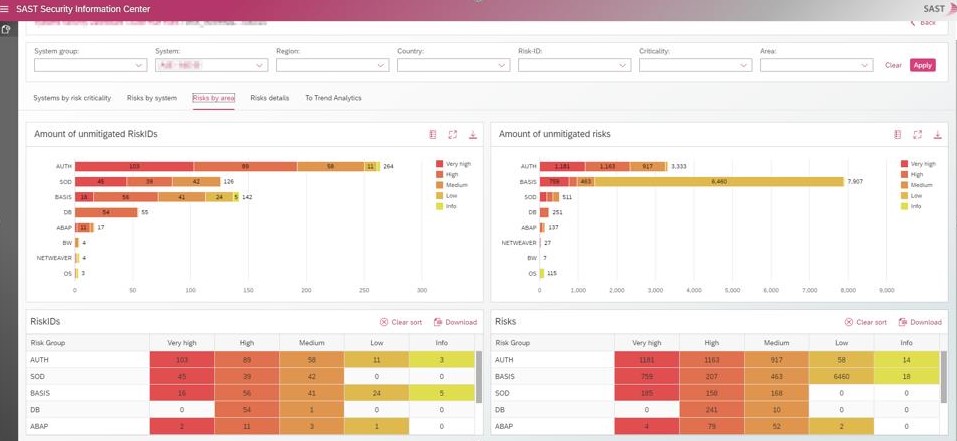
In the SAST SUITE, DÜRR IT Service GmbH found a software tool that provides a central overview of the status of their SAP system landscape, enables them to identify trends, and thanks to its ease of use, is suitable for both specialized teams and management.
Alexander Wirth from DÜRR IT Service GmbH commented on the successful project:
“Thanks to the SAST SUITE, the security status of our system is transparent and plausible at all times. The combination of central system overview and documentation reduces our workload and frees up more time to implement truly relevant measures. In turn, the SAST SUITE lets us clearly identify the success of these new measures, showing it transparently and documented over time. Through real-time monitoring and the alerting options, we can now spot potentially critical behavior proactively and act immediately, instead of simply reacting subsequently.”
If you’re looking for a reliable partner for the real-time protection of your SAP systems, or have any other questions about the SAST SUITE, contact us or visit our website.

Richard Hildebrandt (Junior SAP Consultant, SAST SOLUTIONS)
Tip: For more information about this topic, watch the recording of our webinar “A look at SAP security today: Full transparency with security dashboards”. We’ll be happy to send you the access link.
More about security dashboards:
Security dashboards – Just a buzzword or a true help with the daily security routine?

