 The RFC (Remote Function Call) is the main SAP technology for exchanging data between SAP systems. In addition to standard RFC connections, it is also possible to configure trusted relationships. In our technology tip, find out when you should use trusted system relationships and how you can use them securely.
The RFC (Remote Function Call) is the main SAP technology for exchanging data between SAP systems. In addition to standard RFC connections, it is also possible to configure trusted relationships. In our technology tip, find out when you should use trusted system relationships and how you can use them securely.
Configuring a trusted RFC relationship without password
In contrast to standard connections, a trusted system connection does not require a password to be entered. This greatly simplifies the logon procedure for RFC communication. A connection of this type can be established if the calling system has previously been declared as a “trusted system” to the called system and the called system has also been registered as a “trusting system”. Both SAP systems should have the same security level in this scenario.
During a call, the trusting SAP system checks whether the call was made from a trusted SAP system.
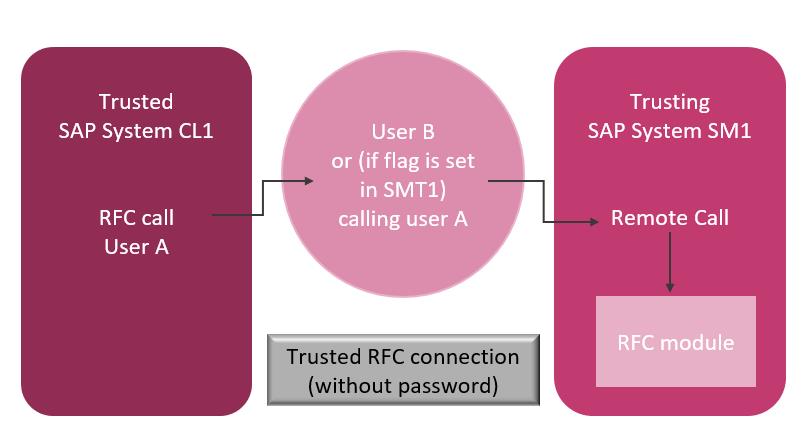
You can use the authorization object S_RFCACL in the target system to control which users are allowed to make calls without entering a password. You can differentiate here by SAP system ID (SAPSID), client, and calling transaction. The logon data of a user can then be verified using the function module AUTHORITY_CHECK_TRUSTED_SYSTEM.
In contrast to standard RFC connections, trusted RFC connections are not created directly in transaction SM59, but instead are tested and maintained using transaction SMT1. When you create a connection to a trusting system, all the necessary information – like the name of the application server and the security key – is provided automatically. Transaction SMT2 enables you to display the trusting systems.
What you need to watch out for when using trusted RFC connections
- You should only use trusted system relationships after a thorough analysis and risk assessment.
- When a Solution Manager is integrated with SAP systems, trusted RFC connections are used as the standard, due to performance reasons. You should check whether this connection type should be replaced with a standard RFC connection, with system user and password, particularly for systems with enterprise-critical data.
- Make sure that the authorization object S_RFCACL does not have any values with “*”.
- The following applies for RFC connections to trusting RFC systems: Do not save any user information, otherwise the trusting system will no longer be able to differentiate between calling users.
- RFC connections should only use technical users or system users that have the authorizations required for this specific purpose – and only these authorizations.
- Do not use trusted connections from systems with low classification levels to systems with higher classification levels.
How you can guarantee secure RFC communication
- If RFC access is made through a trusted system relationship, make sure that the authorization object S_RFCACL has precisely defined which user in the target system is authorized to perform function calls without specifying the password.
- To increase RFC security even more, we recommend checking your SAP Gateway and hardening it, particularly the ACL files secinfo, reginfo, and prxyinfo. For more information, refer to our blog https://sast-solutions.com/blog-en/2019/02/01/step-by-step-secure-sap-gateway/
- We also recommend using Secure Network Communications (SNC) to protect data communication via RFC protocol.
In closing, here’s one more technology tip for you to think about:
The tables RFCDES, RFCTRUST, and RFCSYSACL are used for logging by default. If table logging is activated through the system parameter rec/client=1, you can use the report RSTBHIST or RSVTPROT (or transaction SCU3) to track the changes that have been made to the settings for trusted relationships.
If you need more information about using trusted system relationships or would like to have support in securing your trusted RFC connections, visit our website or e-mail us.

Matthias Anstötz (SAP Security Consultant, SAST SOLUTIONS)
More information on the topic:
One step at a time: How to secure and harden your SAP Gateway

