 A municipal utility company recently implemented a new authorization concept to optimize maintenance, transparency, and user access. The implementation process included an assessment of whether all the existing user master records were really necessary. A major project like implementing a new authorization concept often pays for itself when inactive user master records are classified and restricted, reducing license fees as a result.
A municipal utility company recently implemented a new authorization concept to optimize maintenance, transparency, and user access. The implementation process included an assessment of whether all the existing user master records were really necessary. A major project like implementing a new authorization concept often pays for itself when inactive user master records are classified and restricted, reducing license fees as a result.
Every year, SAP audits its customers’ systems and calculates the user-specific license fee based on the collected data. It is well known that all valid SAP dialog users have an influence on license fees. In this context, “valid” means the time limitation of the respective user master record, not the administrator lock . As such, reducing the number of your valid user master records results in direct, noticeable cost savings. Many companies prefer to leave SAP users active when in doubt, however, out of concern that their day-to-day operations might be disrupted. They fear that a given user ID might still be used technically for background workflows or interface activities. How can you gain insights into user activities in your SAP systems and how can the various user accesses be analyzed efficiently?
No big picture of active SAP users.
Our experience from many customer projects has shown that customers tend to leave SAP users active, out of concern that their processes might be interrupted. This is due primarily to a lack of knowledge regarding direct and indirect usage of user master records. In a system landscape with connected systems, not to mention web scenarios, a login time stamp usually isn’t enough to judge whether a specific user account is needed. External access to data, with a Remote Function Call (RFC) or via web services like SOAP and ODATA, is difficult for companies to keep track of, because they often lack the knowledge and methodology to evaluate these accesses efficiently – particularly since internal dialog accesses by transactions and programs, as well as background processing, have to be taken into account in the big picture.
Analysis options and the difficulty of flexible analysis.
One option for analyzing usage data is the system load monitor (ST03N) with its subfunction “Business Transaction Analysis” (STAD). This transaction lets you analyze the use of the various communication types:
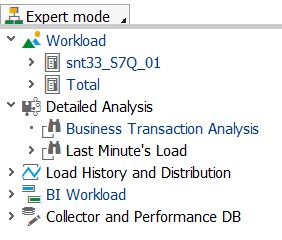
Figure 1: Menu item “Business Transaction Analysis” in the system load monitor
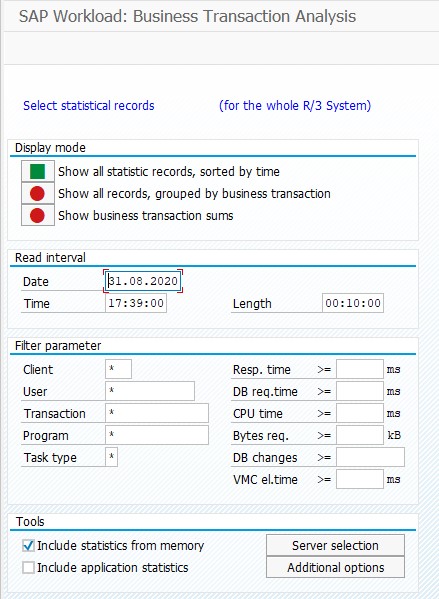
Figure 2: Selection in the Business Transaction Analysis (direct call of transaction STAD)
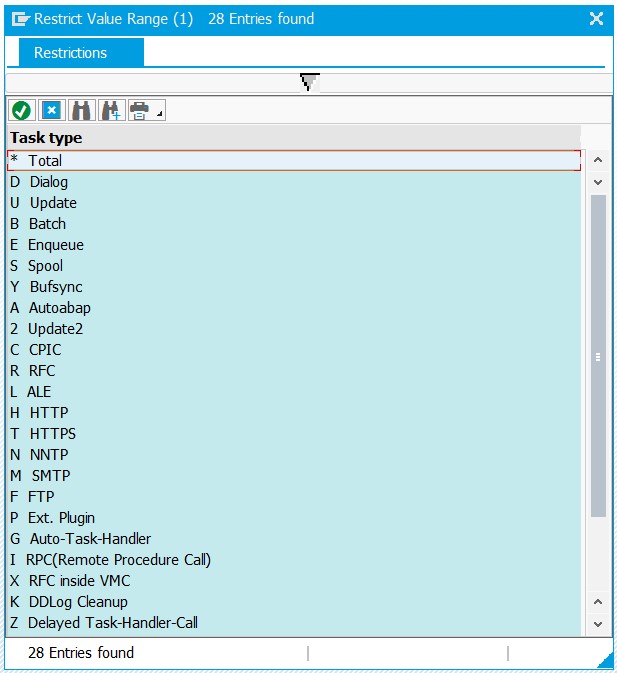
Figure 3: Selection option in the communication type (task type)
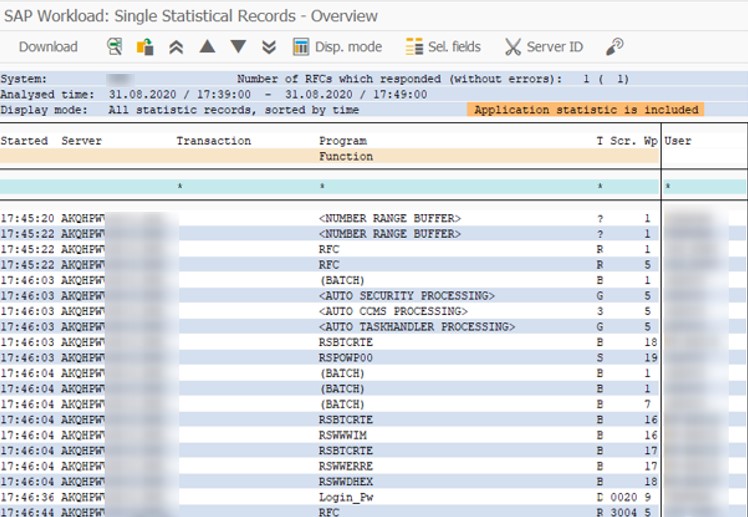
Figure 4: Results list from the Business Transaction Analysis
The analysis shows you which users have generated a system load with the various communication types. From this data, you can derive which users are currently active and which communication types they use, but this analysis is limited to the time frame of a specific day. Longer intervals are especially relevant for usage analyses, especially when you want to draw conclusions about the activities of individual user master records. The system load monitor (ST03N) and its transaction profile gives you another analysis option here. The month-specific examination shows the transactions and program calls that the accounts generally use. You can then double-click an entry to show the users that have used a specific transaction or ABAP program.
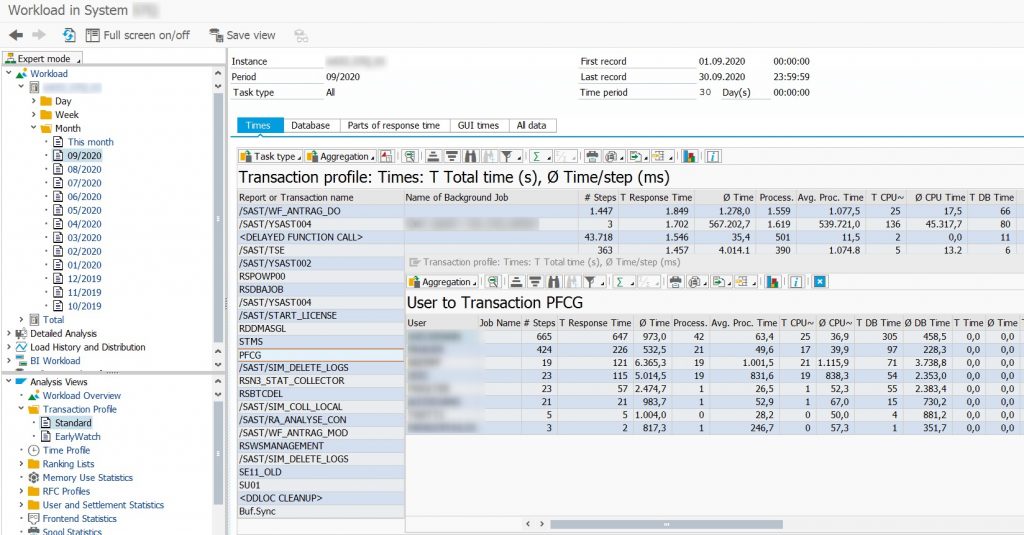
Figure 5: Transaction profile with user view
The challenge here is to combine both data sources and get the big picture. While the standard SAP tools provide the data sources, flexible analyses – at the individual user level, for example – are not possible under this method. As such, you need to manually update and continue analyzing the data to get the pertinent information.
Best practice: transaction usage analysis with the SAST SUITE.
One our customers, a municipal utility in the German state of North Rhine-Westphalia, had a mixture of internal and external access scenarios, but didn’t know which users still uses these scenarios. During the analysis phase of the project, we initially generated an overall view of the accesses, which included every usage level (dialog, batch, RFC, http, and so on). To optimize the analysis time, we used the transaction usage analysis feature of the SAST SUITE. This solution analyzes the usage by all active users, based on the CCMS alert monitor. Since all levels of communication with the system are examined in this approach, it is possible to develop a comprehensive, user-specific view over a longer time period. The access frequency is also displayed, classified in levels A through D.
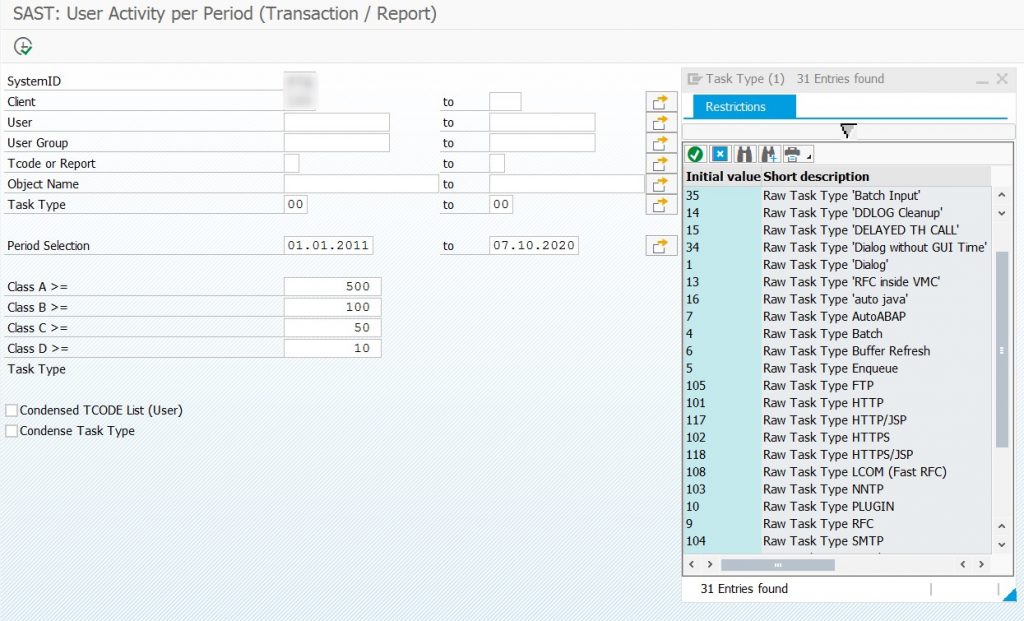
Figure 6: SAST transaction usage analysis with the SAST SUITE
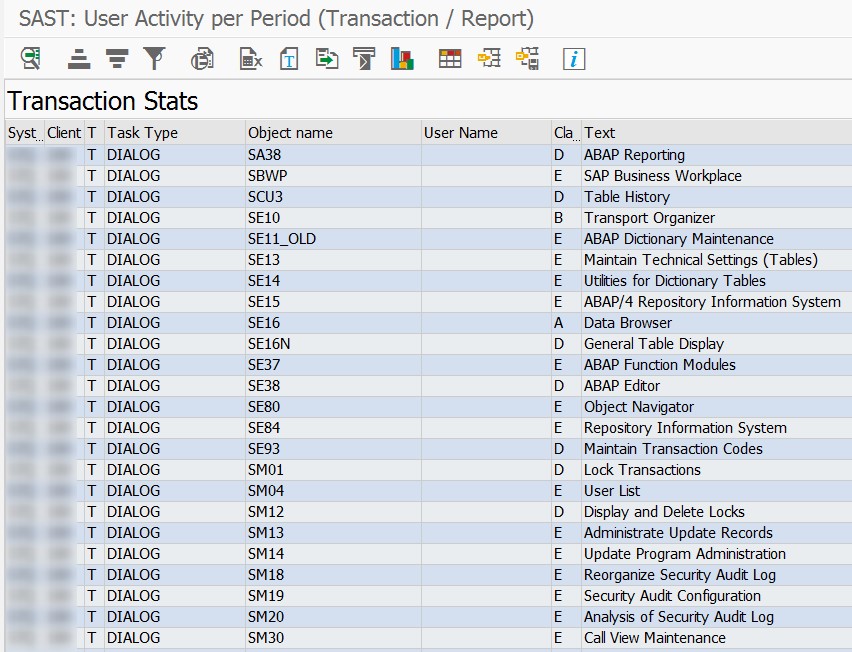
Figure 7: Results list from SAST transaction usage analysis with the SAST SUITE
25% inactive user master records mean significantly lower license fees in future.
The results list from this analysis quickly gave our customer the overall picture for every single user, including technical users, which were also included. The activity period for the analysis was defined as six months: users that didn’t have any trace of system activities during this time period were considered candidates for removal.
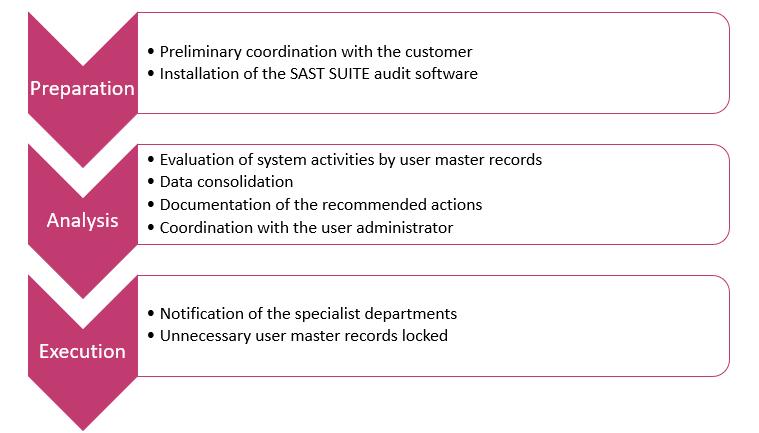
The result: thanks to the end-to-end analysis using SAST SUITE tools, recommended actions could be derived and user IDs removed safely, without any negative side-effects for current operations. The project was able to identify nearly 25% of the 1,350 analyzed user master records as inactive and the accounts could be restricted. This was a win-win for the customer, which was able to optimize its SAP license fees with very little effort and generate an immediate, significant return on investment.
The optimized procedure at a glance:
If you’re interested in restricting your inactive user master records to reduce your license fees, we can give you the support you need to do so quickly and efficiently. Find out more on our SAST SOLUTIONS website and, if we’ve piqued your interest, send us an e-mail.

Steffen Maltig (Head of SAP Consulting, SAST SOLUTIONS
FURTHER INFORMATION ON THIS TOPIC:
Are your SAP licensing costs really optimized?
Speed up development of framework and application authorization concepts for SAP ERP and S/4HANA

